[ad_1]
MOVEit, the file-transfer software program exploited in latest weeks in one of many greatest cyberattacks ever, has acquired yet one more safety replace that fixes a essential vulnerability that could possibly be exploited to provide hackers entry to huge quantities of delicate information.
On Thursday, MOVEit maker Progress Software program printed a safety bulletin that included fixes for 3 newly found vulnerabilities within the file-transfer utility. Essentially the most severe of them, tracked as CVE-2023-36934, permits an unauthenticated attacker to realize unauthorized entry to the appliance database. It stems from a safety flaw that permits for SQL injection, one of many oldest and most typical exploit courses.
The vulnerability comprises the identical parts—and, seemingly, the identical probably devastating penalties—as one which got here to gentle in late Might when members of the Clop ransomware crime syndicate started mass-exploiting it on weak networks world wide. Thus far, the Clop offensive has hit 229 organizations and spilled information affecting greater than 17 million folks, in response to statistics tracked by Brett Callow, an analyst with safety agency Emsisoft. Casualties embody Louisiana and Oregon DMVs, the New York Metropolis Division of Training, and vitality corporations Schneider Electrical and Siemens Electrical.
There are not any identified reviews of the brand new vulnerability coming beneath energetic exploitation, however given its severity and previous expertise, Progress Software program and safety practitioners are urging all MOVEit customers to put in it straight away. Apart from CVE-2023-36934, Thursday’s safety replace patches two extra vulnerabilities. All of them have been found by safety companies HackerOne and Development Micro.
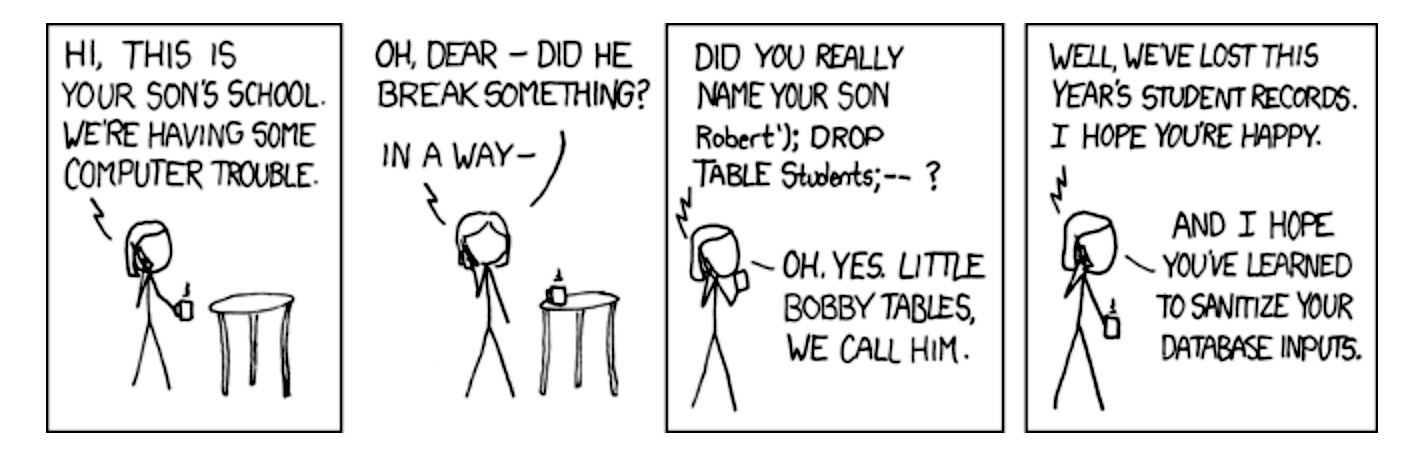
Builders, meet Bobby Tables
One factor that makes CVE-2023-36934 and the sooner vulnerability exploited by Clop so essential is that they are often exploited by folks once they’re not even logged in to the system they’re hacking. Each additionally stem from bugs that enable for SQL injection, a vulnerability class with a protracted historical past of abuse. Usually abbreviated as SQLi, it stems from a failure by an internet utility to correctly question backend databases. SQL syntax makes use of apostrophes to point the start and finish of a knowledge string. The apostrophes enable SQL parsers to differentiate between information strings and database instructions.
Improperly written net apps can typically interpret inputted information as instructions. Hackers can exploit these errors by coming into strings that embody apostrophes or different particular characters into net fields that trigger backend databases to do issues the builders by no means meant to do. These types of assaults have shaped the premise for a number of the greatest compromises in historical past. Apart from the latest Clop spree, two different notable examples embody the 2007 hack of Heartland Fee Programs that allowed convicted hacker Albert Gonzalez to make off with information for 130 million bank cards and the 2011 compromise of HBGary.
SQL injection is the subject of an xkcd cartoon that includes Bobby Tables, a scholar whose full title is “Robert’); DROP TABLE College students;–?” (with out the citation marks). When the college pc system tries to course of his title, it interprets solely “Robert” as information and processes the “DROP TABLE” as the damaging SQL command to delete information. Because of this, the college loses a whole yr’s price of data.
A second vulnerability fastened in Thursday’s MOVEit safety replace can be the results of SQLi bugs. Progress Software program stated it “may enable an authenticated attacker to realize unauthorized entry to the MOVEit Switch database. An attacker may submit a crafted payload to a MOVEit Switch utility endpoint which may end in modification and disclosure of MOVEit database content material.”
The third vulnerability fastened, CVE-2023-36933, permits hackers to terminate the MOVEit utility unexpectedly. The latter two vulnerabilities carry a severity described as excessive.
The vulnerabilities have an effect on a number of MOVEit Switch variations, from 12.0.x to fifteen.0.x. Given the injury that resulted from Clop’s mass exploitation of the sooner MOVEit vulnerability, the most recent patches ought to be put in as quickly as potential. Sorry, admins, but when that requires working late on a Friday or over the weekend, that’s the higher choice than waking as much as a world of harm on Monday morning.
[ad_2]
Source_link













