[ad_1]

Getty Pictures
After years of being outmaneuvered by snarky ransomware criminals who tease and brag about every new sufferer they declare, worldwide authorities lastly bought their likelihood to show the tables, they usually aren’t squandering it.
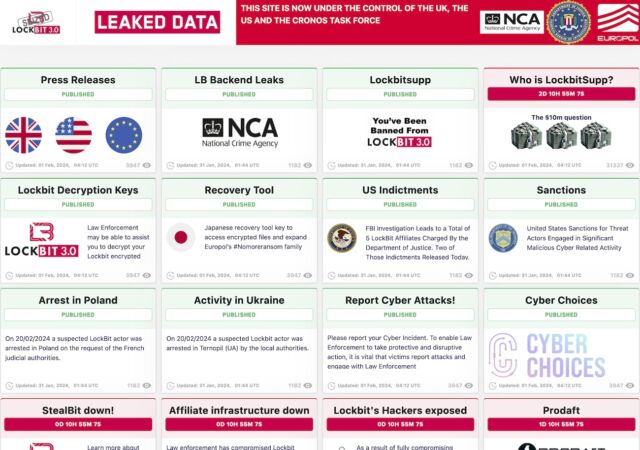
The highest-notch trolling got here after authorities from the US, UK, and Europol took down many of the infrastructure belonging to LockBit, a ransomware syndicate that has extorted greater than $120 million from hundreds of victims world wide. On Tuesday, many of the websites LockBit makes use of to disgrace its victims for being hacked, strain them into paying, and brag of their hacking prowess started displaying content material saying the takedown. The seized infrastructure additionally hosted decryptors victims might use to get well their knowledge.
this_is_really_bad
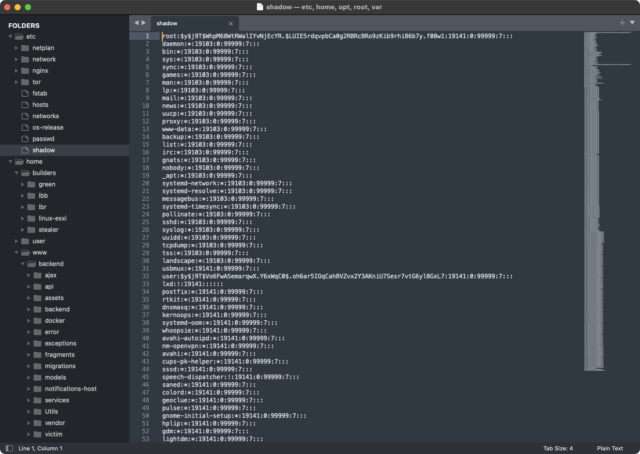
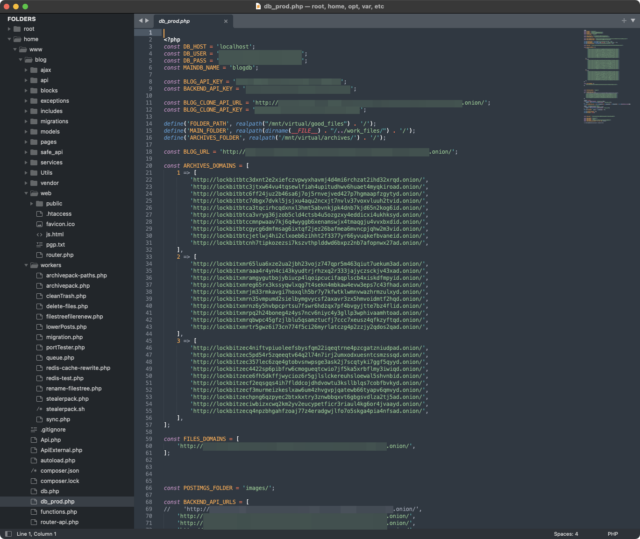
Authorities didn’t use the seized name-and-shame web site solely for informational functions. One part that appeared prominently gloated over the extraordinary extent of the system entry investigators gained. A number of pictures indicated that they had management of /and many others/shadow, a Linux file that shops cryptographically hashed passwords. This file, among the many most security-sensitive ones in Linux, might be accessed solely by a consumer with root, the best stage of system privileges.
Different pictures demonstrated that investigators additionally had full management of the primary net panel and the system LockBit operators used to speak with associates and victims.
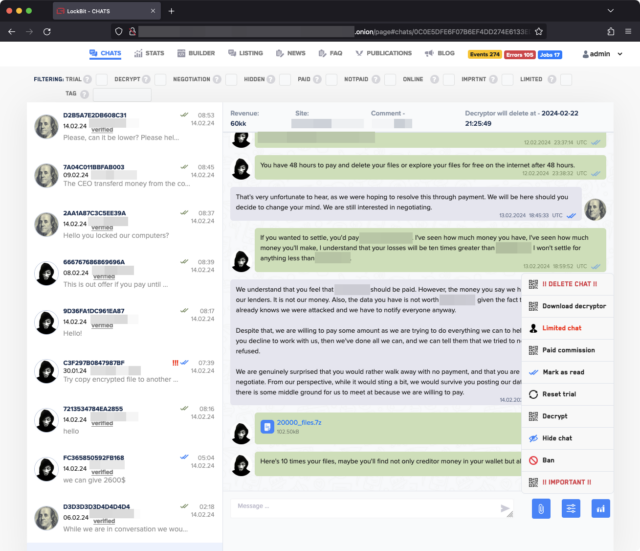
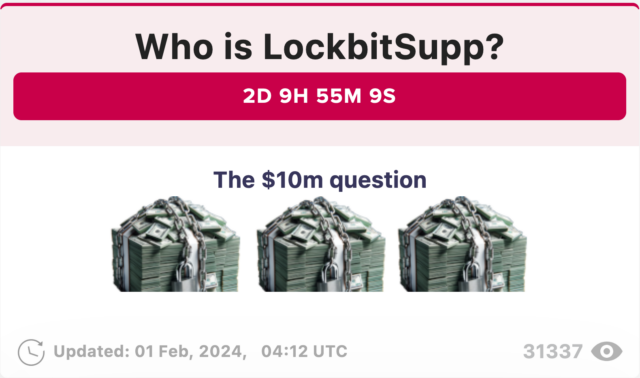
The razzing didn’t cease there. File names of the photographs had titles together with: “this_is_really_bad.png,” “oh expensive.png,” and “doesnt_look_good.png.” The seized web page additionally teased the upcoming doxing of LockbitSupp, the moniker of the primary LockBit determine. It learn: “Who’s LockbitSupp? The $10m query” and displayed pictures of money wrapped in chains with padlocks. Copying a standard apply of LockBit and competing ransomware teams, the seized web site displayed a clock counting down the seconds till the figuring out info will likely be posted.
In all, authorities mentioned they seized management of 14,000 accounts and 34 servers positioned within the Netherlands, Germany, Finland, France, Switzerland, Australia, the US, and the UK. Two LockBit suspects have been arrested in Poland and Ukraine, and 5 indictments and three arrest warrants have been issued. Authorities additionally froze 200 cryptocurrency accounts linked to the ransomware operation.
“At current, an enormous quantity of knowledge gathered all through the investigation is now within the possession of regulation enforcement,” Europol officers mentioned. “This knowledge will likely be used to help ongoing worldwide operational actions centered on focusing on the leaders of this group, in addition to builders, associates, infrastructure, and prison belongings linked to those prison actions.”
LockBit has operated since a minimum of 2019 underneath the identify “ABCD.” Inside three years, it was probably the most broadly circulating ransomware. Like most of its friends, LockBit operates underneath what’s generally known as ransomware-as-a-service, wherein it supplies software program and infrastructure to associates who use it to compromise victims. LockBit and the associates then divide any ensuing income. Tons of of associates participated.
In keeping with KrebsOnSecurity, one of many LockBit leaders mentioned on a Russian-language crime discussion board {that a} vulnerability within the PHP scripting language supplied the means for authorities to hack the servers. That element led to a different spherical of razzing, this time from fellow discussion board individuals.
“Does it imply that the FBI supplied a pen-testing service to the associates program?” one participant wrote, in response to reporter Brian Krebs. “Or did they resolve to participate within the bug bounty program? :):).”
A number of members additionally posted memes taunting the group in regards to the safety failure.
“In January 2024, LockBitSupp informed XSS discussion board members he was upset the FBI hadn’t provided a reward for his doxing and/or arrest, and that in response he was inserting a bounty on his personal head—providing $10 million to anybody who might uncover his actual identify,” Krebs wrote. “‘My god, who wants me?’ LockBitSupp wrote on January 22, 2024. ‘There may be not even a reward out for me on the FBI web site.’”
[ad_2]
Source_link













